Checking someone out before you meet them face-to-face isn’t paranoia; it’s basic risk management. Think of it like property search logic: you never trust the sales pitch alone, you verify the facts.
I don’t walk into deals based on “vibes,” and neither should you. Whether it’s a date, a marketplace purchase, a sublet inquiry, or a potential business partner you found online, the downside risk is real. The cost to mitigate it? Usually just five minutes and a bit of discipline.
For instance, if someone provides an address for a pickup or meeting, a quick reverse address lookup can confirm the location exists and matches their story. If the formatting is odd or the address is incomplete, a reverse address finder can clean it up so you aren’t validating the wrong spot. If documents show slightly different addresses, a search can highlight those inconsistencies before you ever show up.
Most people skip this because it feels awkward. Then they get surprised when the story doesn’t match the person. In higher-stakes situations – like a sublet or a business arrangement – a limited search including public property data from Texas to Florida can add necessary context. The goal isn’t to invade someone’s private life, but to ensure the location is real, consistent, and logical for the situation.
This guide focuses on practical identity verification – enough to avoid obvious fraud, catfishing, and high-risk scenarios. We aren’t talking about stalking, doxxing, or digging for dirt. Just confirming the basics, spotting inconsistencies early, and structuring the first meeting so you stay in control.
Define Your Safety Threshold Before You Search
Before you open a single search tool, decide what “safe enough” actually looks like for you. Investors do this instinctively: assess the risk first, look at the upside second.
Know What You’re Walking Into
A daytime coffee in a crowded café is one risk profile. Inviting someone into your home, sharing travel plans, handing over keys, or sending money? That’s a completely different animal.
Use a simple scale to categorize the interaction:
- Low Risk: Public meetup, short duration, no money exchanged.
- Medium Risk: Buying/selling items, first-time service work, repeated meetups.
- High Risk: Roommates, caregivers, business partners, large payments, or granting access to your home.
Once you’ve categorized the risk, write down your verification goal. Literally just one line.
Examples:
- “Confirm real name + city + consistent identity.”
- “Confirm this person actually works where they claim.”
- “Confirm there aren’t obvious, current court/public-record issues.”
That is your finish line. Without a clear goal, people either spiral into endless digging or skip verification entirely.
Ground Rules: Info Control + Behavior Tells
Two simple rules can save you a lot of headaches:
- Don’t overshare early. Hold off on giving your home address, workplace routines, financial details, or travel schedule until you’re comfortable with who you’re dealing with.
- Keep chats on-platform initially. Platforms have moderation, reporting, and transaction protections. Moving off-platform quickly is often a pressure tactic.
And yes, trust your gut. Not because “intuition is magic,” but because behavior is data. If the person gets pushy, angry, evasive, or tries to rush you past your own rules, that conflict is the red flag. You don’t debate it. You exit.
Digital Detective Work: What to Check
You aren’t doing espionage. You are checking for consistency.
Click to expand for tool details Public Records and People Search
People-search sites and public-record portals can help confirm:
- A name plausibly exists in a given area.
- Age range and location roughly align.
- There is a consistent trail across time.
For higher-stakes situations (roommates, caregivers, serious partnerships), people often step up to more formal background screening where it is legal and appropriate.
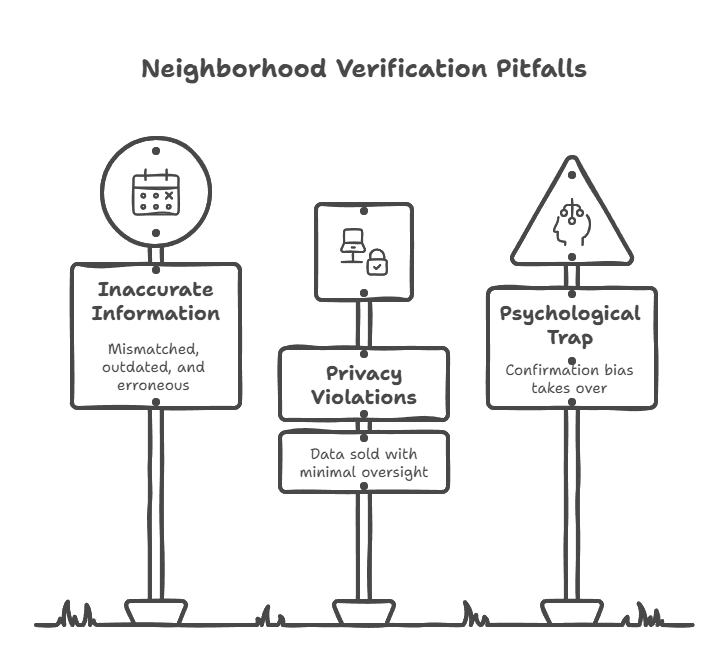
Important Limits:
- These databases can be wrong, incomplete, or delayed.
- You are looking for patterns and deal-breakers, not trying to litigate someone’s life from a web page.
Ethical Note: Use this responsibly. If your “verification” is really about collecting personal data you don’t need, stop. That is how safety routines turn into harassment.
Phone, Email, and Social Checks
Contact info is useful because it is hard to fake cleanly for long periods.
- A reverse phone lookup can sometimes confirm whether a number is aligned with the claimed region/name (or flagged in scam complaints).
- A reverse email lookup can surface linked accounts or public mentions.
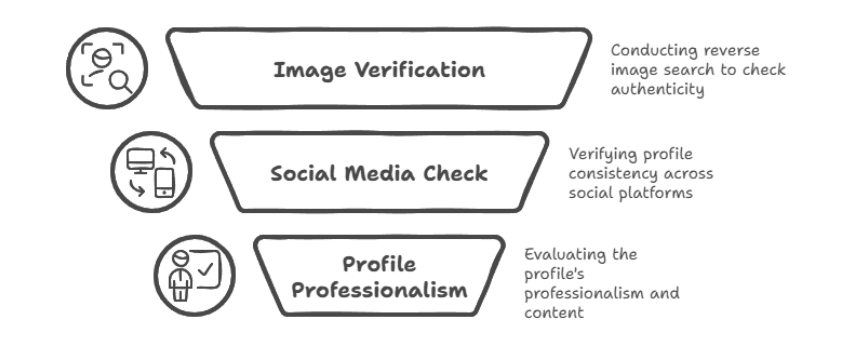
Then, do a simple social scan across major platforms. You aren’t grading their personality. You are checking for a coherent identity:
- Photos that aren’t obviously stolen.
- A timeline that looks normal.
- A work/education story that roughly matches what they told you.
- Mutual connections (if applicable) who exist and look real.
Watch for loud, repeated signals:
- Bragging about scams.
- Violent threats.
- Harassment patterns.
- A trail of angry disputes tied to sales/transactions.
One weird post isn’t evidence. Repeated behavior is.
Deep Footprint Dives (OSINT)
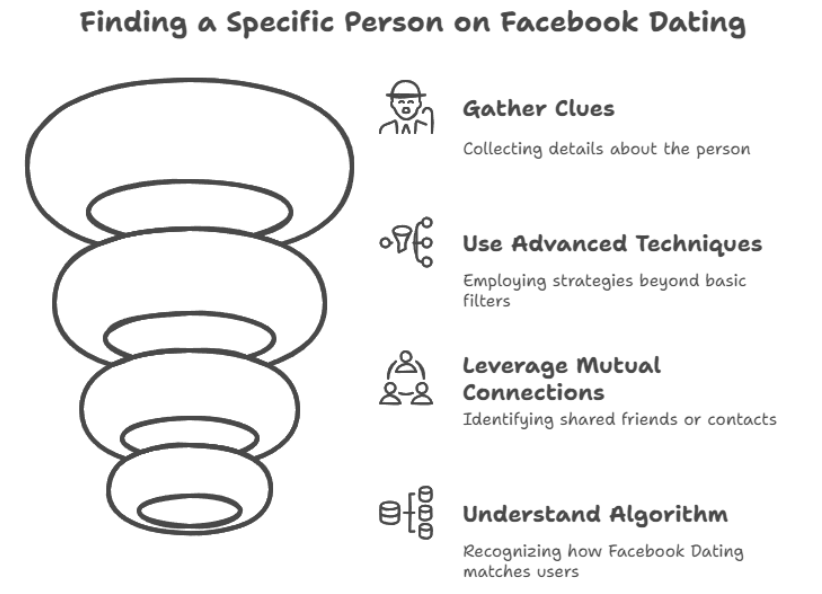
If you are dealing with high-stakes scenarios – large transactions, formal partnerships, someone gaining access to your home – deeper digital footprint analysis can help connect identities across usernames and platforms.
Most people don’t need this most of the time. Treat it like a fire extinguisher: good to have, not something you play with daily.
The Verification Checklist
Tools don’t protect you. Process does.
The Standard Workflow
Use this sequence to verify consistency:
- Get the basics. Name + city. If relevant: employer or business name.
- Run a quick consistency check. Does the name + area produce plausible matches, or is it a dead end?
- Cross-check contact info. Phone/email should not point to a totally different identity or obvious scam pattern.
- Social/work scan. Look for normal timelines and consistency (LinkedIn can help for business contexts).
- Video call for remote/online-first situations. Five minutes beats five hours. If someone refuses a basic video call while demanding urgency, that is data.
Low-risk meetups should take minutes to verify. Higher-risk scenarios justify deeper verification – but only with a clear reason and within legal boundaries.
Handling Red Flags and Gaps
Here are the red flags that actually matter:
- Zero verifiable footprint plus refusal to answer basic questions.
- Inconsistent names across platforms with no clean explanation.
- Obviously stolen/stock photos.
- Contact info tied to scam complaints or repeated “buyer beware” reports.
- Pressure tactics: rush, guilt, anger, secrecy.
Some gaps are normal:
- Common names.
- Minimal social presence.
- Privacy-conscious people who keep a small footprint.
So don’t be paranoid. Be decisive. If you can’t verify critical facts and the person won’t help you verify them, you don’t meet. Full stop. “No” is a complete sentence.
Executing the First Meetup
Verification isn’t the finish line. It’s the filter.
Safer First Meetings
Treat the first meeting like a controlled test:
- Location: Public place, lots of people.
- Communication: Tell a friend where you’ll be + set a check-in time.
- Substances: Limit alcohol.
- Transport: Control your transportation (you can leave anytime).
- Home: Do not invite someone to your home as the “first meeting” default.
If the risk is higher, bring someone with you – or don’t meet at all. You are not obligated to “be nice” at your own expense.
Continuing Verification Over Time
For ongoing arrangements, due diligence is ongoing too. People reveal themselves through consistency:
- Do their stories stay stable?
- Do they keep commitments?
- Do new claims check out?
Trust is earned over time. Verification just makes sure you aren’t handing trust to someone who can’t clear a basic honesty bar.
Final Thoughts: Five Minutes Now Beats a Mess Later
Here’s the whole play in one line: set your baseline, verify for consistency, then meet on your terms.
If you turn this into a simple checklist you run anytime you’re meeting someone from an app, a marketplace, or a networking intro, you cut your exposure to catfishing, scams, and avoidable risk fast. Your safety is worth five minutes.